11 Types of Spoofing Attacks Every Security Professional Should
Por um escritor misterioso
Descrição
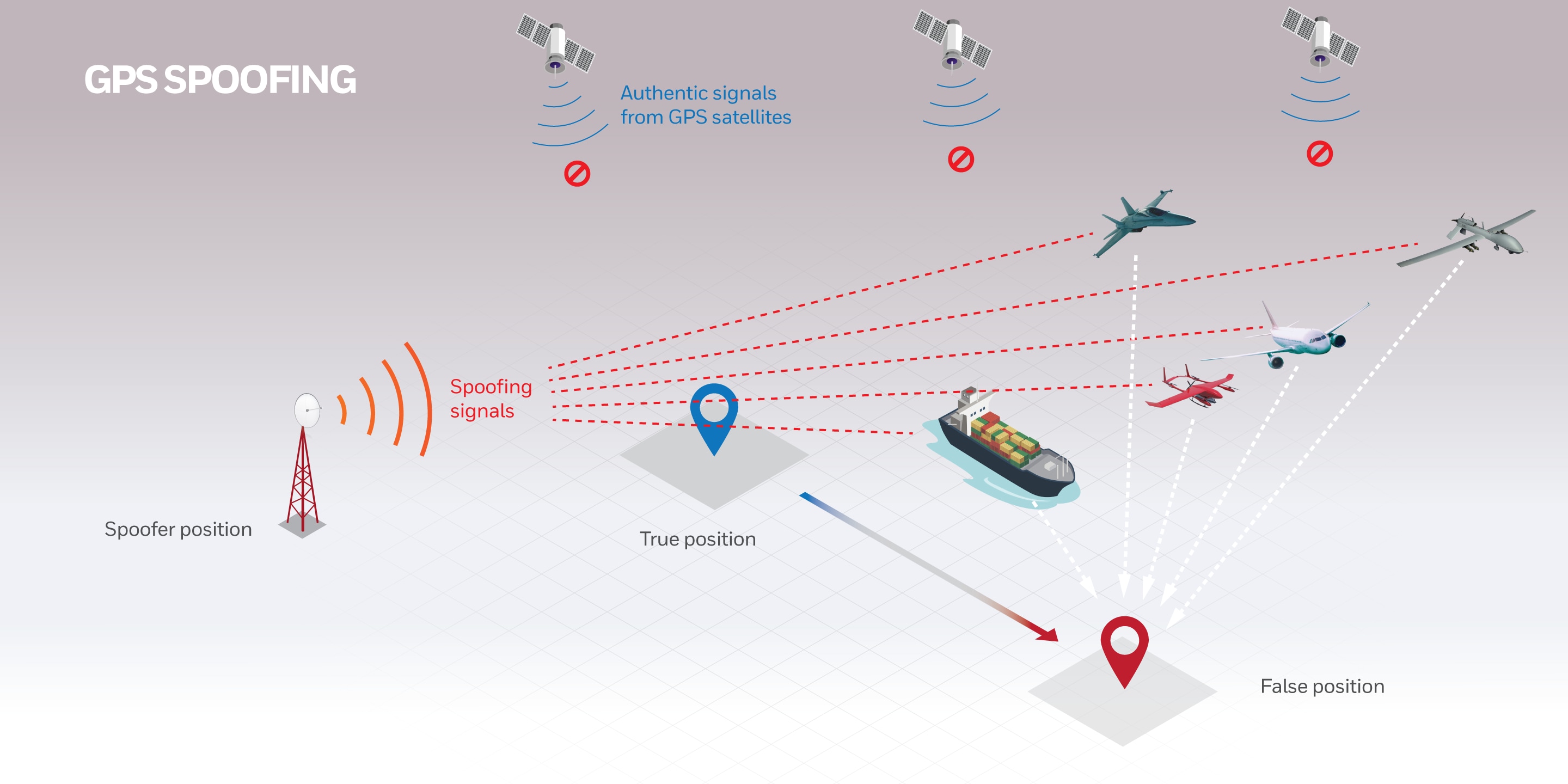
The term “spoofing” might have a comic implication in some contexts, but it’s no joke when it comes to information security. In fact, this is a subject matter of a whole separate chapter in a seasoned cybercriminal’s handbook. It comprises a multitude of techniques aimed at camouflaging a malicious actor or device as somebody or something else. The goal is to feign trust, gain a foothold in a system, get hold of data, pilfer money, or distribute predatory software. What can black hats try to . . .
The term “spoofing” might have a comic implication in some contexts, but it’s no joke when it comes to information security. In fact, this is a subject matter of a whole separate chapter in a seasoned cybercriminal’s handbook. It comprises a multitude of techniques aimed at camouflaging a malicious actor or device as somebody or something else. Out of all the nefarious scenarios that fit the mold of a spoofing attack, the following 11 types are growingly impactful for the enterprise these days.

Phishing Statistics 2020 - Latest Report

Must Know Phishing Statistics In 2023 - Attacks And Breaches

How do Phishing and Spoofing Attacks Impact Businesses?
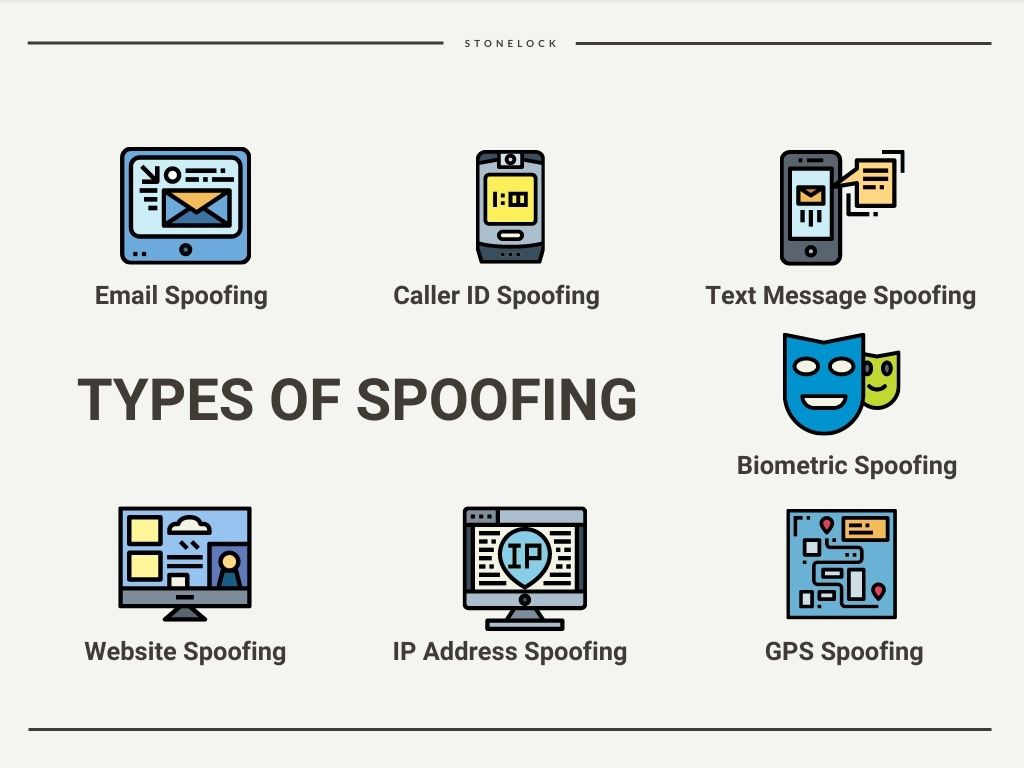
What Is Spoofing? And How To Avoid An Attack - StoneLock

Don't Be Fooled By A Spoofing Attack
Awareness Of Different Types Of Spoofing Attacks Can Keep Your

6 Common Phishing Attacks and How to Protect Against Them
Sensors, Free Full-Text

10 top anti-phishing tools and services

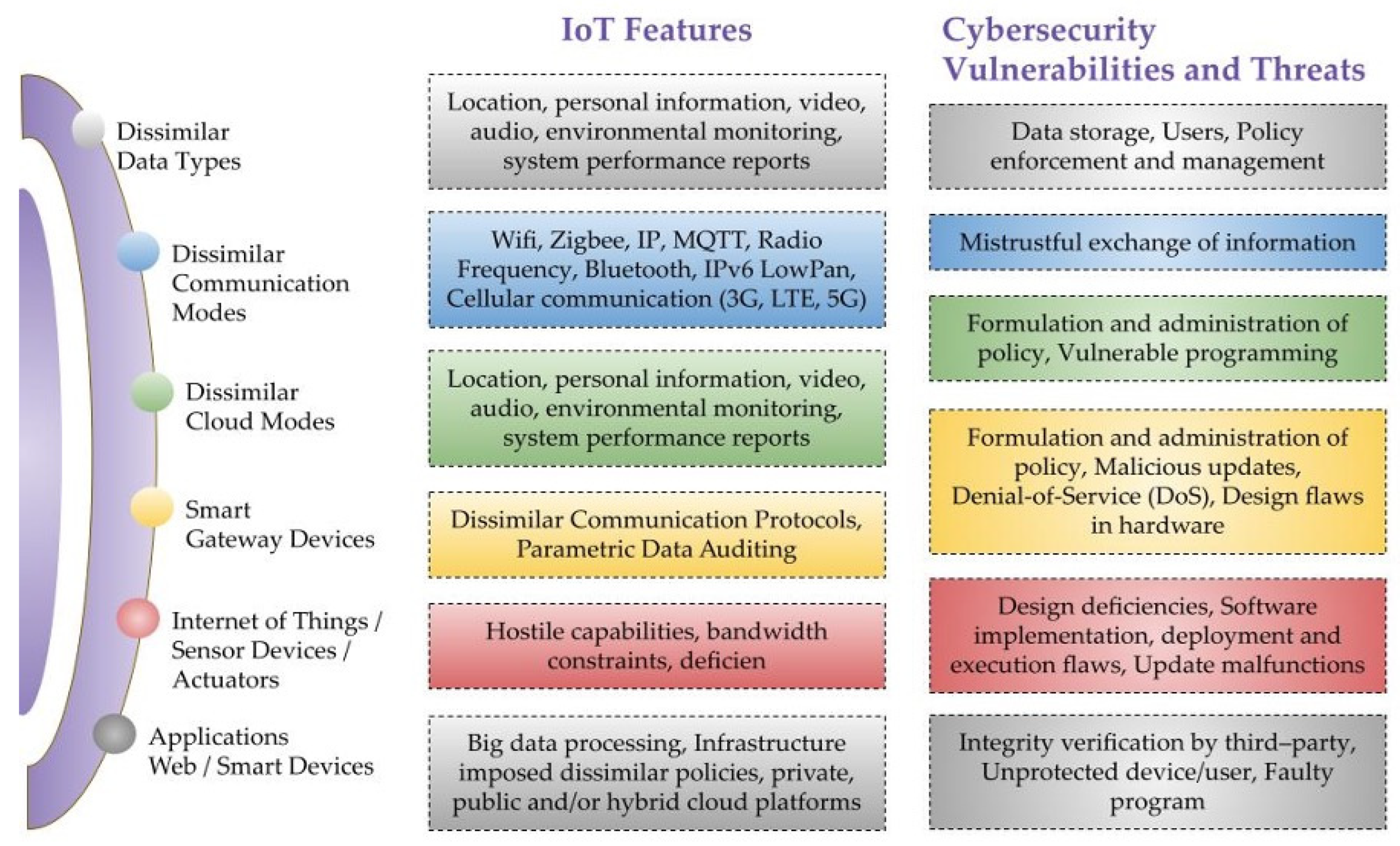
Attack Methods and Solutions [11].

Spoofing Attacks, Spoofing Vs Phishing

What Is Spoofing? - Cisco
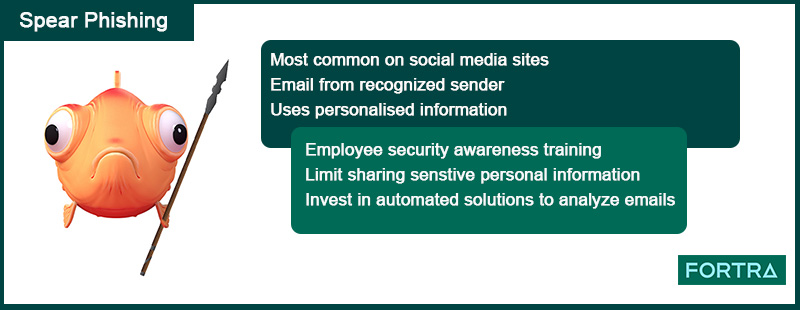
6 Common Phishing Attacks and How to Protect Against Them
de
por adulto (o preço varia de acordo com o tamanho do grupo)