Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Descrição
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.
Tampering and Reverse Engineering on iOS - OWASP MASTG

PDF) Reverse Engineering for Malicious Code Behavior Analysis using Virtual Security Patching
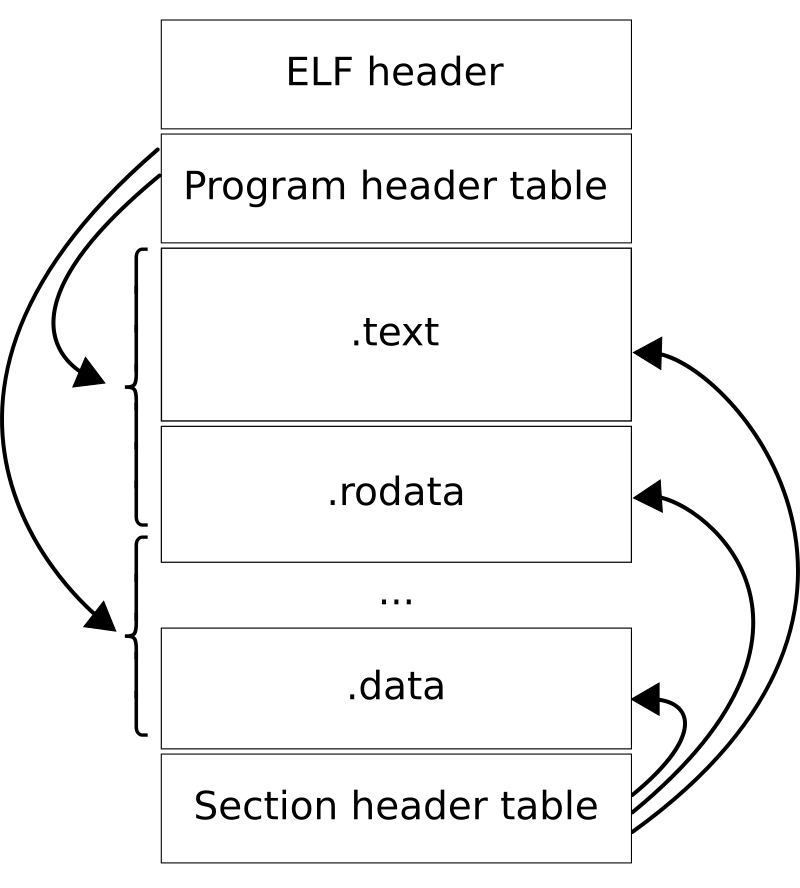
Executable and Linkable Format - Wikipedia

2022-2023 College Catalog by Honolulu Community College - Issuu
Apple Debugging L8 - Reverse Engineering Basics
Advanced Apple Debugging & Reverse Engineering

Tampering and Reverse Engineering on iOS - OWASP MASTG
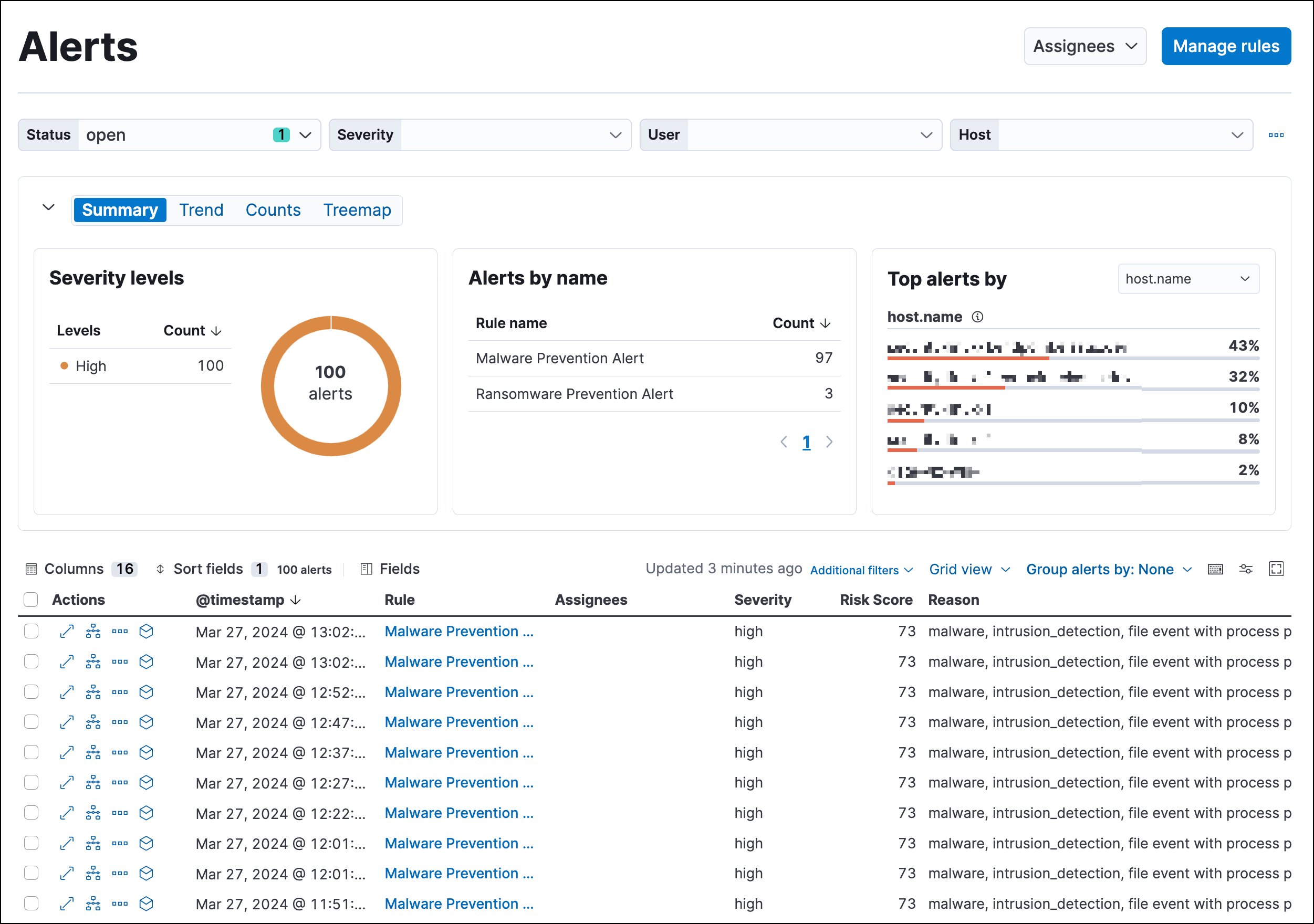
Detections and alerts, Elastic Security Solution [8.11]

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
How to Reverse Engineer an iOS App, by Zafar Ivaev

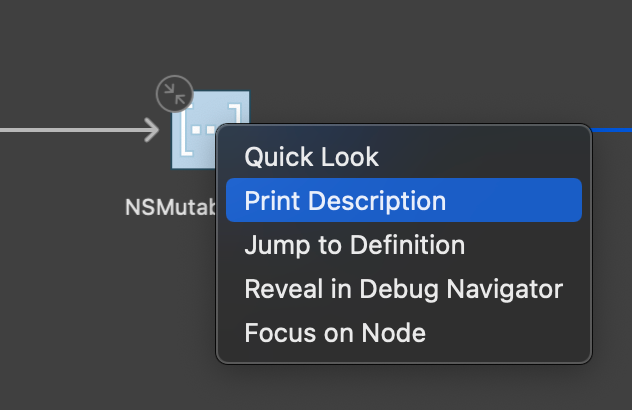
Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
de
por adulto (o preço varia de acordo com o tamanho do grupo)