Cross-Site Scripting Attacks and Defensive Techniques: A
Por um escritor misterioso
Descrição
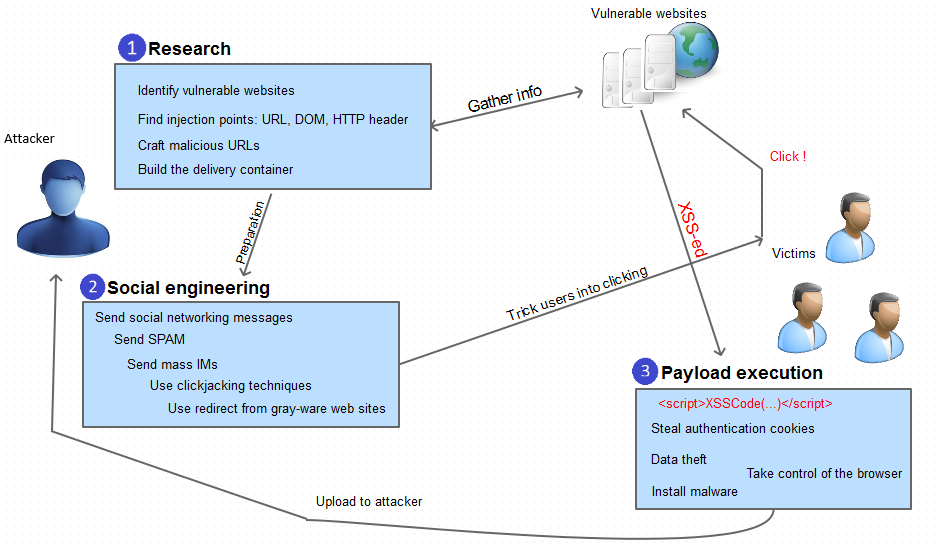
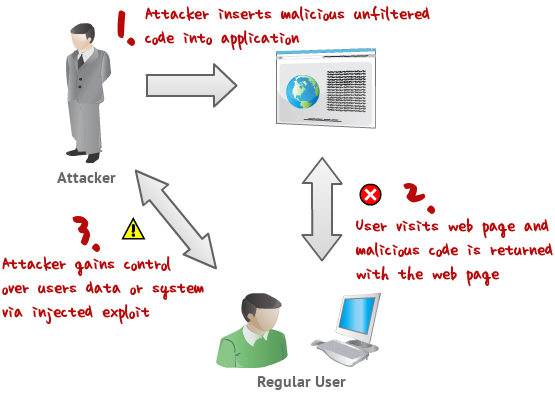
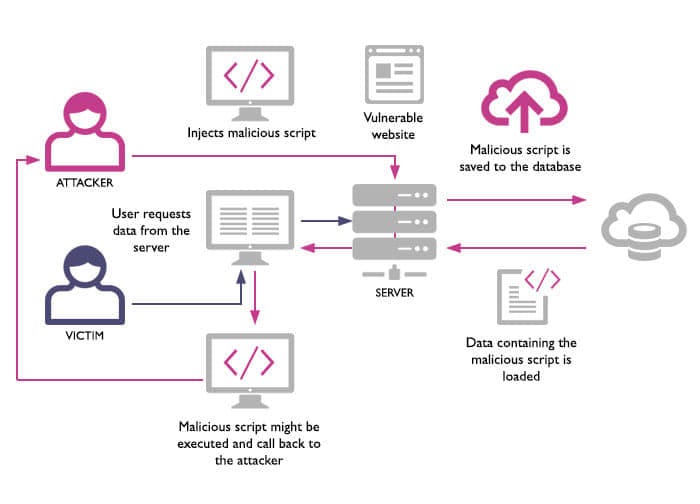
The advancement of technology and the digitization of organizational functions and services have propelled the world into a new era of computing capability and sophistication. The proliferation and usability of such complex technological services raise several security concerns. One of the most critical concerns is cross-site scripting (XSS) attacks. This paper has concentrated on revealing and comprehensively analyzing XSS injection attacks, detection, and prevention concisely and accurately. I have done a thorough study and reviewed several research papers and publications with a specific focus on the researchers’ defensive techniques for preventing XSS attacks and subdivided them into five categories: machine learning techniques, server-side techniques, client-side techniques, proxy-based techniques, and combined approaches. The majority of existing cutting-edge XSS defensive approaches carefully analyzed in this paper offer protection against the traditional XSS attacks, such as stored and reflected XSS. There is currently no reliable solution to provide adequate protection against the newly discovered XSS attack known as DOM-based and mutation-based XSS attacks. After reading all of the proposed models and identifying their drawbacks, I recommend a combination of static, dynamic, and code auditing in conjunction with secure coding and continuous user awareness campaigns about XSS emerging attacks.

SQL injection and cross-site scripting: The differences and attack anatomy

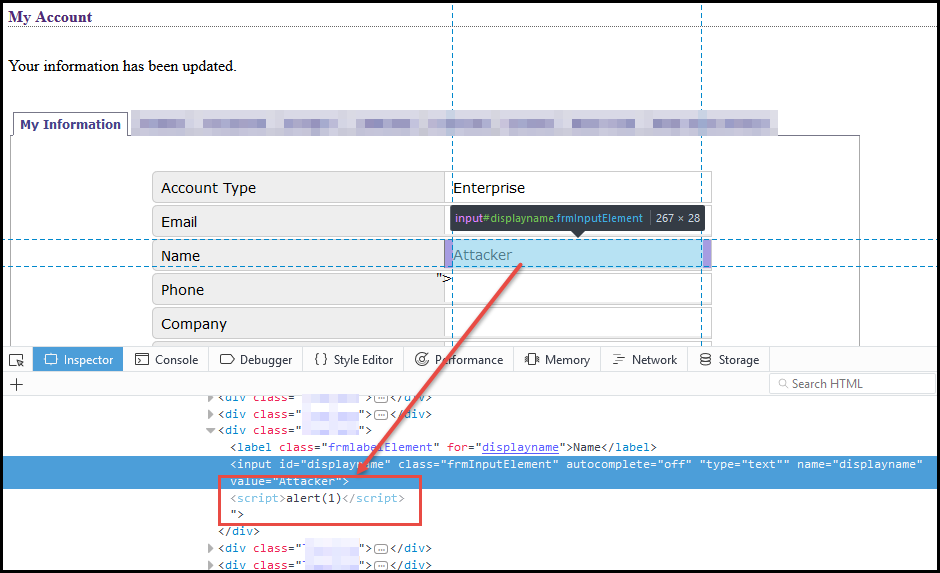
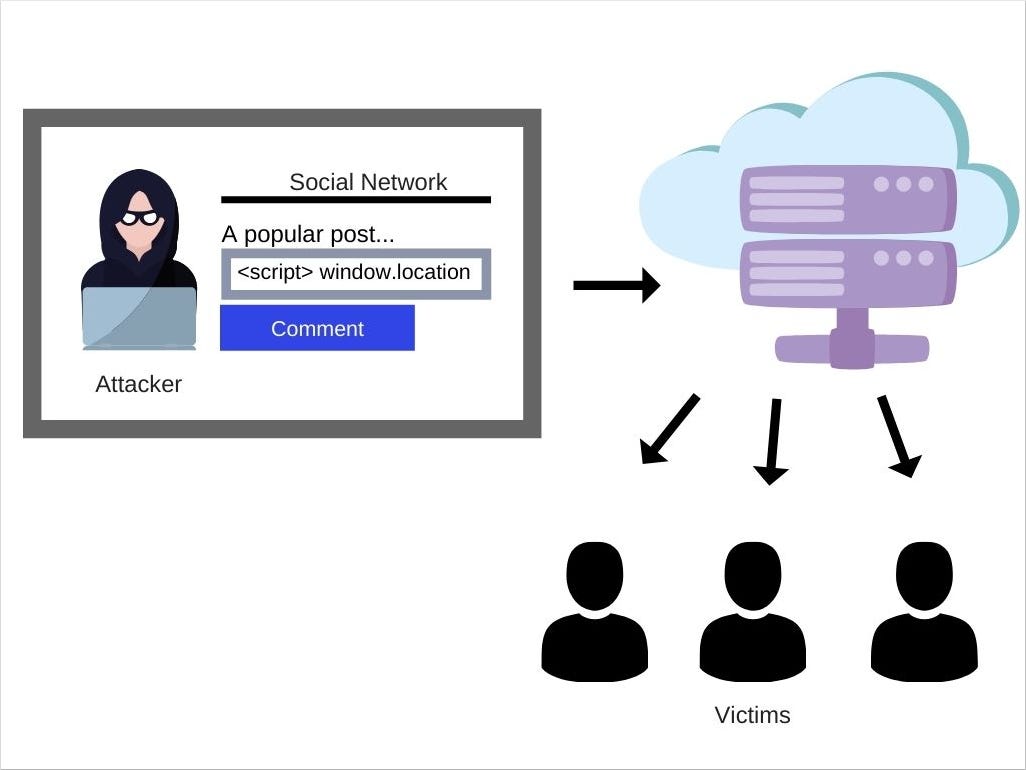
Cross-site scripting (XSS)
What Is Persistent XSS
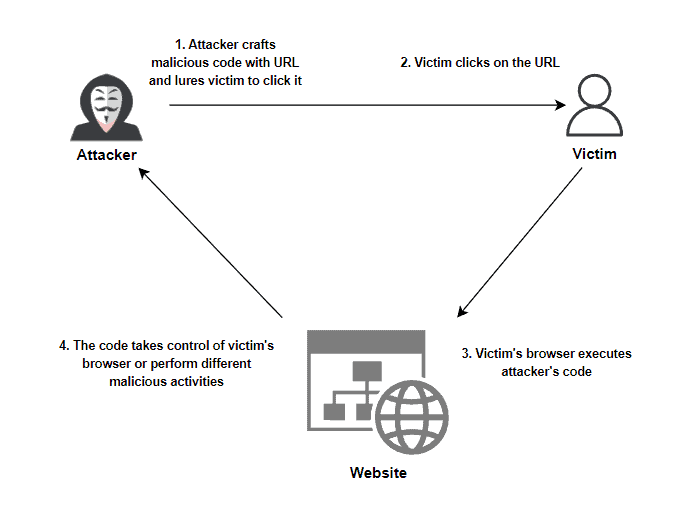
Cross-Site Scripting (XSS) Explained
What Is Cross Site Scripting and How to Avoid XSS Attacks?

What is XSS? Cross-site scripting attacks explained
XSS Tutorial

What Is Cross-Site Scripting (XSS)?
What is Cross-Site Scripting. Summary, by MRunal

What is cross-site scripting (XSS)?, Tutorial & examples
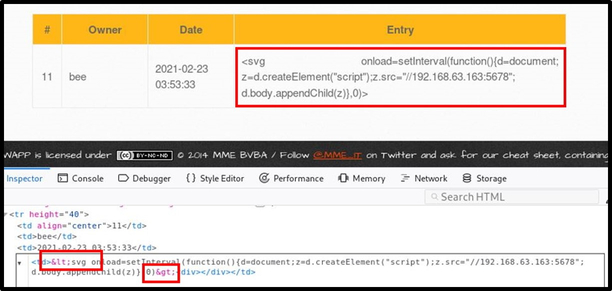
Using an Interactive Cross-site Scripting Backdoor

PDF) Exploitation of Cross-Site Scripting (XSS) Vulnerability on Real World Web Applications and its Defense
de
por adulto (o preço varia de acordo com o tamanho do grupo)