PDF] Power Consumption-based Detection of Sabotage Attacks in
Por um escritor misterioso
Descrição
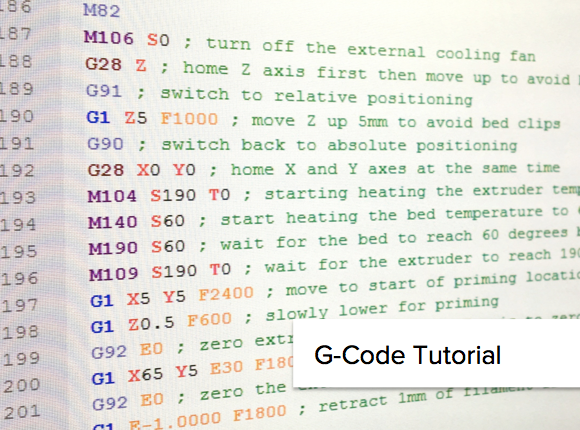
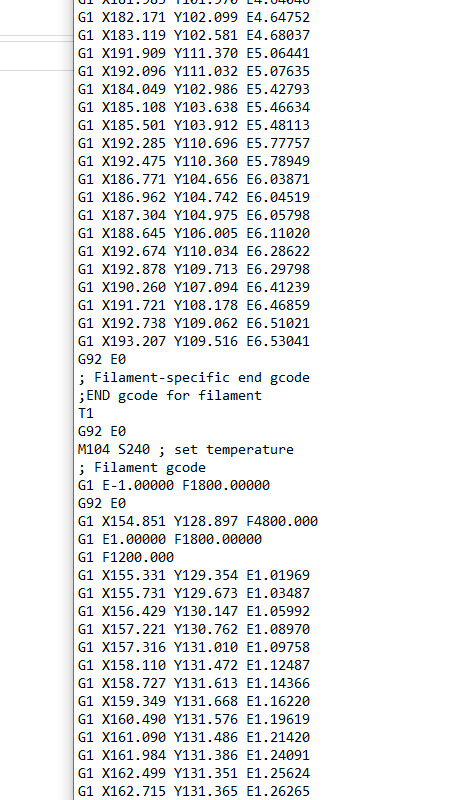
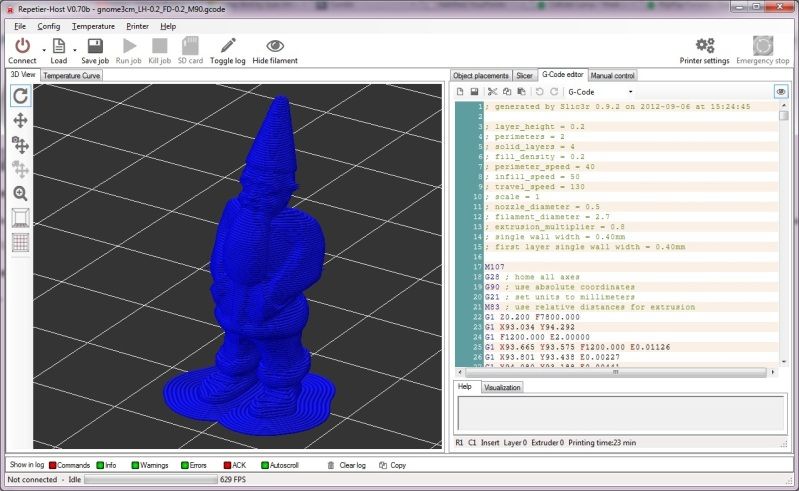
This work proposes a novel approach for detecting sabotage attacks in additive Manufacturing, based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. Additive Manufacturing (AM), a.k.a. 3D Printing, is increasingly used to manufacture functional parts of safety-critical systems. AM's dependence on computerization raises the concern that the AM process can be tampered with, and a part's mechanical properties sabotaged. This can lead to the destruction of a system employing the sabotaged part, causing loss of life, financial damage, and reputation loss. To address this threat, we propose a novel approach for detecting sabotage attacks. Our approach is based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. The proposed approach has numerous advantages: (i) it is non-invasive in a time-critical process, (ii) it can be retrofitted in legacy systems, and (iii) it is airgapped from the computerized components of the AM process, preventing simultaneous compromise. Evaluation on a desktop 3D Printer detects all attacks involving a modification of X or Y motor movement, with false positives at 0%.
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pubs.acs.org/cms/10.1021/acsnano.1c10635/asset/images/acsnano.1c10635.social.jpeg_v03)
Nanotechnology Tools Enabling Biological Discovery
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pyimagesearch.com/wp-content/uploads/2022/08/cv-electricity-featured.png)
Computer Vision and Deep Learning for Electricity - PyImageSearch
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.mandiant.com/sites/default/files/inline-images/hacktivist-ot-fig5.png)
We (Did!) Start the Fire: Hacktivists Increasingly Claim Targeting of OT Systems
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/9-Table1-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.imperva.com/learn/wp-content/uploads/sites/13/2021/10/cyberwarfare.png)
What is Cyber Warfare, Types, Examples & Mitigation
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://citrap.scholasticahq.com/article/36186-the-critical-pathway-to-insider-risk-model-brief-overview-and-future-directions/attachment/91555.png)
The Critical Pathway to Insider Risk Model: Brief Overview and Future Directions
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pub.mdpi-res.com/computers/computers-12-00256/article_deploy/html/images/computers-12-00256-g005.png?1702023399)
Computers, Free Full-Text
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.frontiersin.org/files/Articles/884192/frai-05-884192-HTML-r1/image_m/frai-05-884192-g001.jpg)
Frontiers Recommendations for ethical and responsible use of artificial intelligence in digital agriculture
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/13-Figure9-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://img.yumpu.com/24279199/1/500x640/comparing-insider-it-sabotage-and-espionage-a-model-cert.jpg)
Comparing Insider IT Sabotage and Espionage: A Model - Cert
de
por adulto (o preço varia de acordo com o tamanho do grupo)