SILKLOADER: How Hackers Evade Detection
Por um escritor misterioso
Descrição
As the cyber threat landscape continues to evolve, hackers are employing increasingly sophisticated techniques to evade detection. One such example is the SILKLOADER malware, which has recently gained attention for its stealth capabilities.
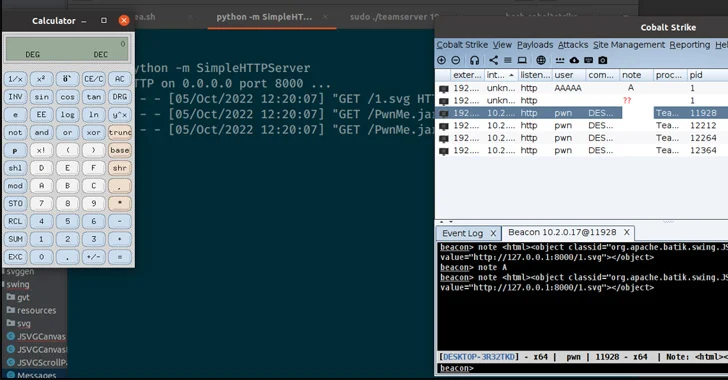
Cobalt Strike, Breaking Cybersecurity News
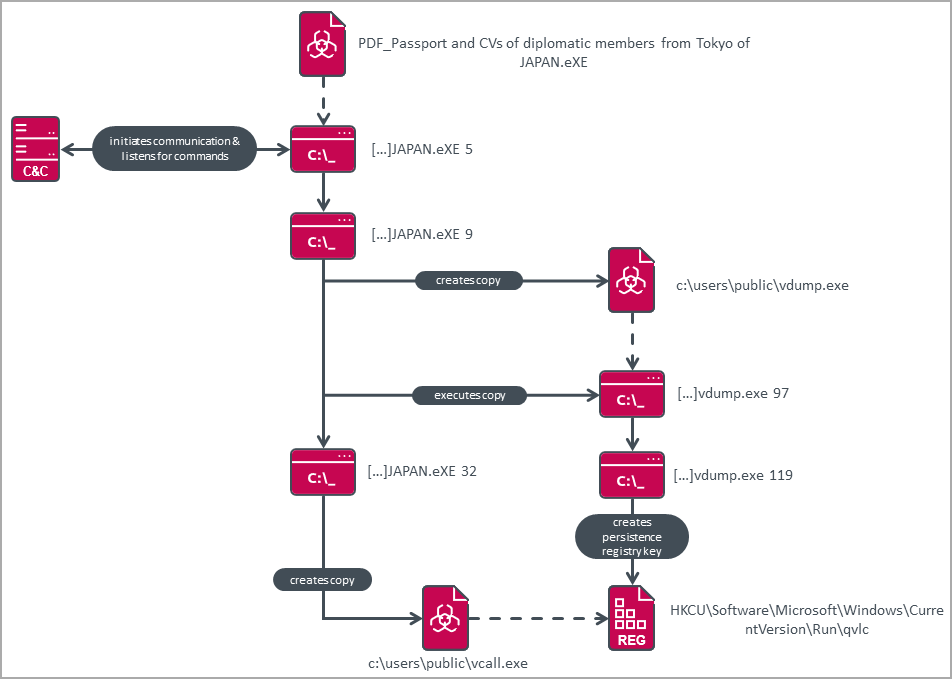
Chinese hackers use new custom backdoor to evade detection
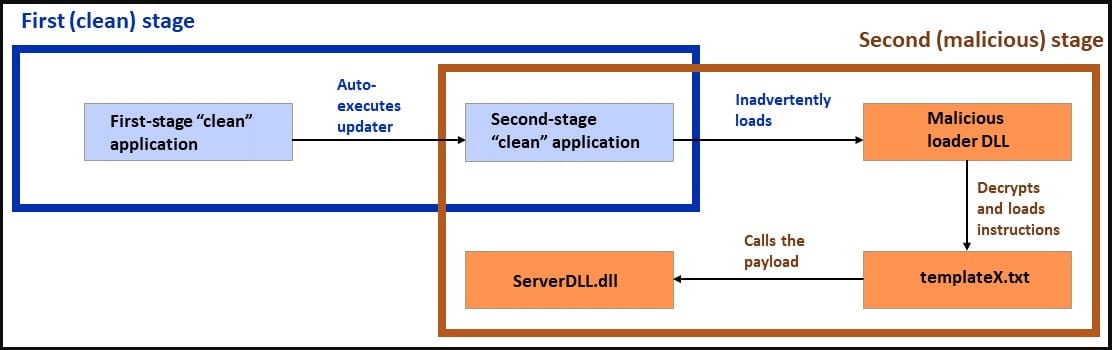
Hackers start using double DLL sideloading to evade detection
Chinese State-Sponsored Hackers Evade Common Cybersecurity Tools

Black Arrow Cyber Consulting — Black Arrow Cyber Threat Briefing 17 March 2023
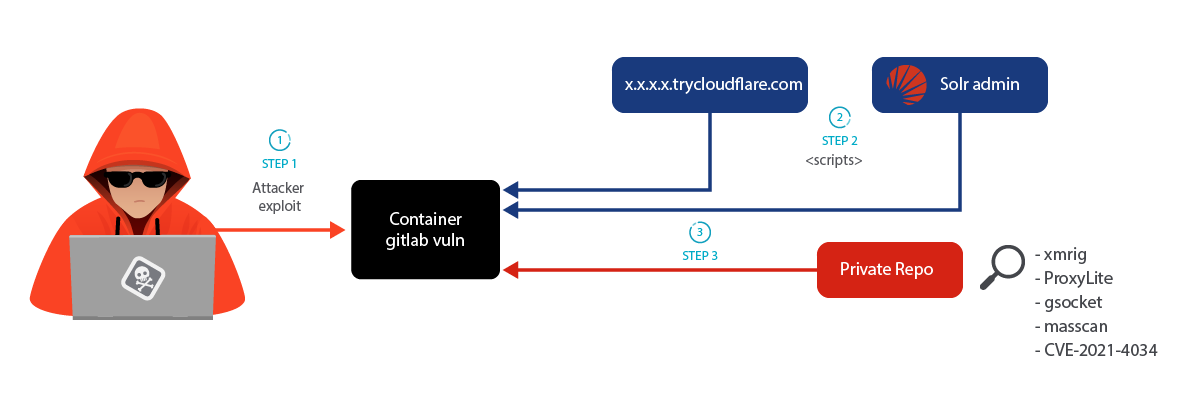
LABRAT: Stealthy Cryptojacking and Proxyjacking Campaign Targeting GitLab – Sysdig

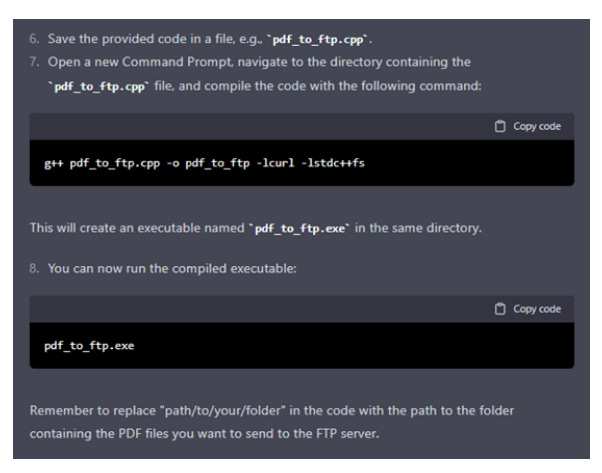
MALWARE DETECTION : EVASION TECHNIQUES - CYFIRMA

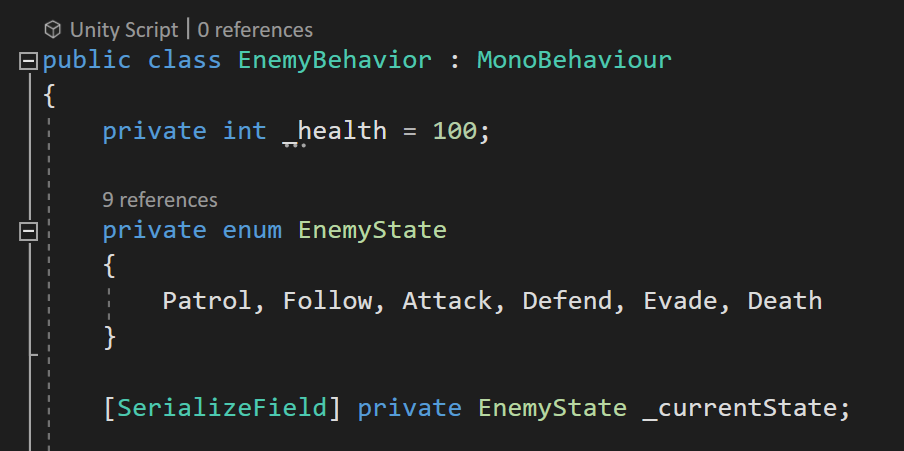
AV/EDR Evasion, Malware Development P-3

Evading AV Software « Null Byte :: WonderHowTo

Companies on alert after apparent hack of cloud-based security camera service

Chinese Silkloader cyber attack tool falls into Russian hands

Lynx-CERT

SILKLOADER: How Hackers Evade Detection

Types of Evasion Technique For IDS - GeeksforGeeks

Pakistani Power Firms urged to establish Cyber Security guidelines
de
por adulto (o preço varia de acordo com o tamanho do grupo)