Stop Compromising Developer Security with Phone Numbers - Website
Por um escritor misterioso
Descrição
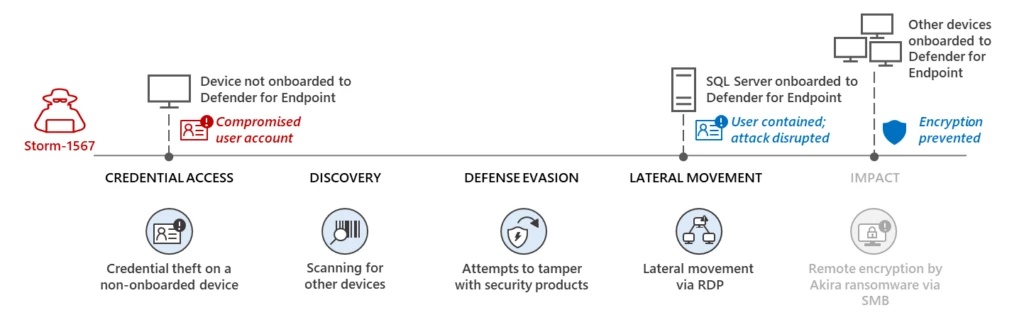
Automatic disruption of human-operated attacks through containment

Cisco Secure Email Threat Defense - Cisco

End of Life Software: Risks, Dangers & What to Do Next
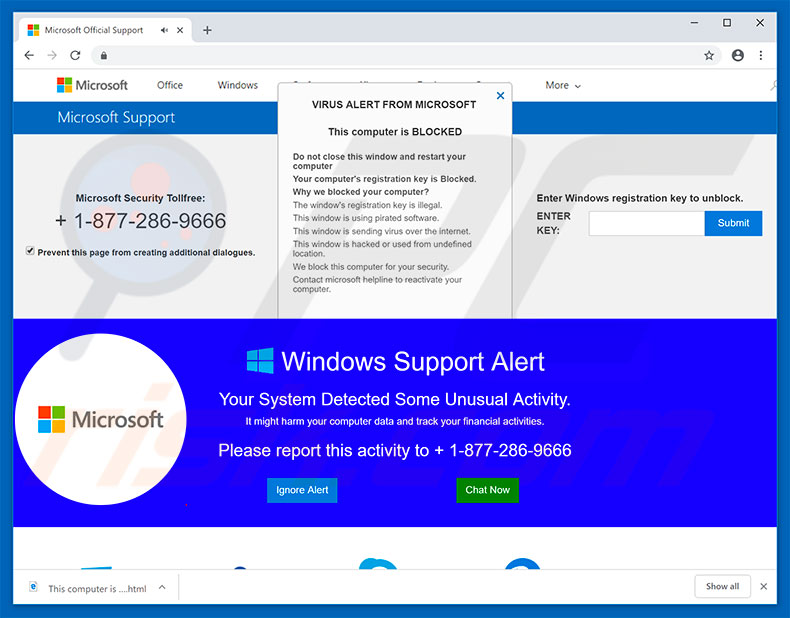
Microsoft Support Alert POP-UP Scam - Removal and recovery steps
Fix WordPress Redirect Hack: Stop Redirects to Spam Sites

Software supply chain threats Software supply chain security
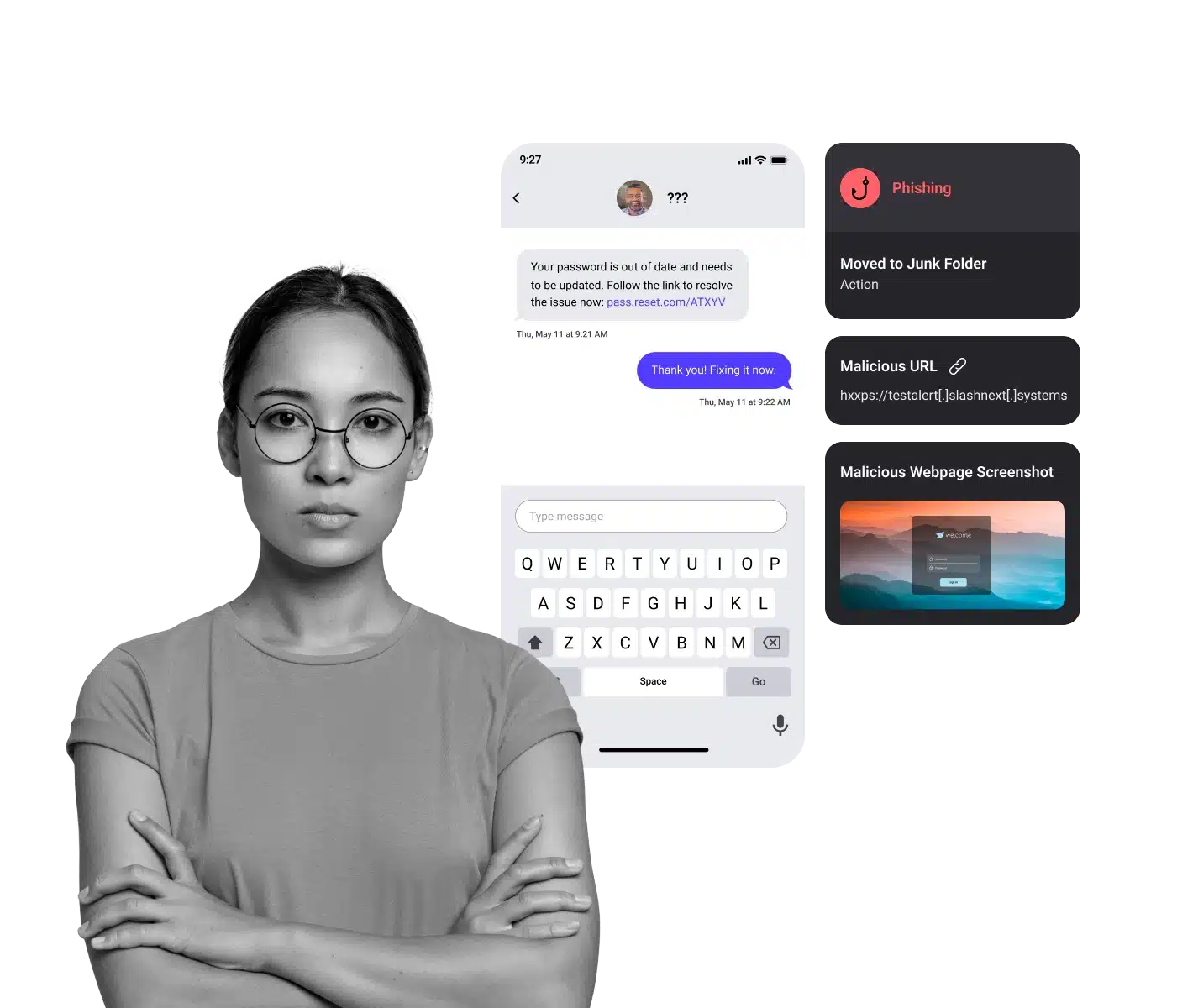
Complete Generative AI Security for Email, Mobile, and Browser

Tokenization (data security) - Wikipedia

Z-JAK Tech Newsletter October 2023 by Z-JAK Technologies - Issuu
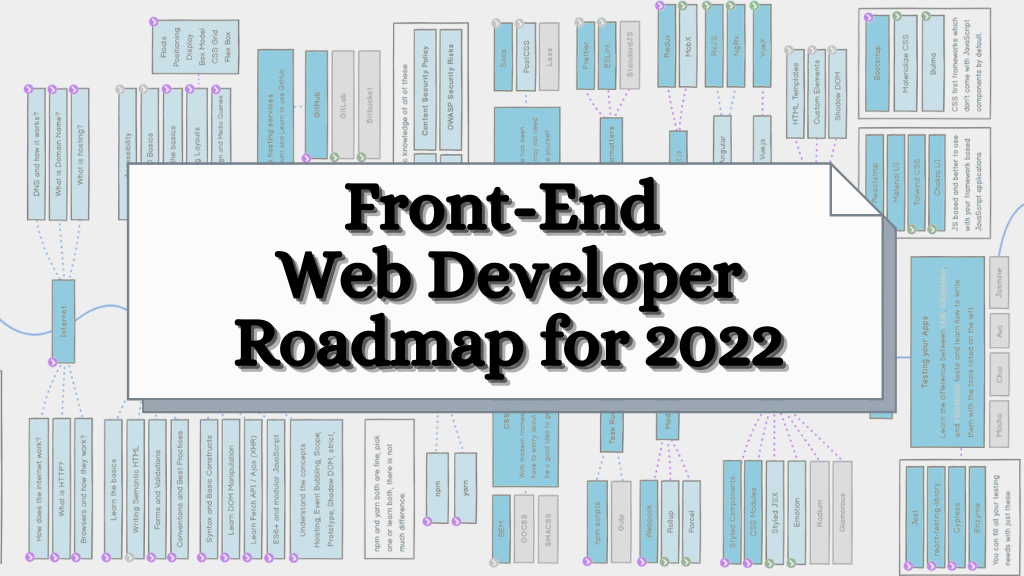
Front-End Developer RoadMap for 2022

What Is Credential Stuffing? How To Prevent Credential Stuffing

Denial-of-service attack - Wikipedia
de
por adulto (o preço varia de acordo com o tamanho do grupo)